What are the types of malware? How does malware spread? How do you know if you’re infected? We've got answers.

What is malware?
Malware, short for malicious software, is a blanket term for viruses, worms, trojans and other harmful computer programs hackers use to wreak destruction and gain access to sensitive information. In other words, software is identified as malware based on its intended malicious use, rather than a particular technique or technology used to build it.
This means that the question of, say, what the difference is between malware and a virus misses the point a bit: a virus is a type of malware, so all viruses are malware (but not every piece of malware is a virus).
History of malware
Malware has a long, storied history, dating back to infected floppy disks swapped by Apple II hobbyists in the 1980s and the Morris Worm spreading across Unix machines in 1988.
Some other high-profile malware attacks over the years have included:
- ILOVEYOU, a worm that spread like wildfire in 2000 and did more than $15 billion in damage
- SQL Slammer, which ground internet traffic to a halt within minutes of its first rapid spread in 2003
- Conficker, a worm that exploited unpatched flaws in Windows and leveraged a variety of attack vectors – from injecting malicious code to phishing emails – to ultimately crack passwords and hijack Windows devices into a botnet.
- Zeus, a late ’00s keylogger Trojan that targeted banking information
- CryptoLocker, the first widespread ransomware attack, whose code keeps getting repurposed in similar malware projects
- Stuxnet, an extremely sophisticated worm that infected computers worldwide but only did real damage in one place: the Iranian nuclear facility at Natanz, where it destroyed uranium-enriching centrifuges, the mission it was built for by U.S. and Israeli intelligence agencies
- Ryuk, ransomware that targets vulnerable organizations that are likely to pay a ransom, including hospitals and governments. It is typically distributed via the TrickBot trojan.
For a deep dive into the history of malware, see 11 infamous malware attacks: The first and the worst.
How do malware infections happen?
Malware infections happen in two phases: First there is the initial infection (how the malware gets onto a computer or network) and then the malware spreads.
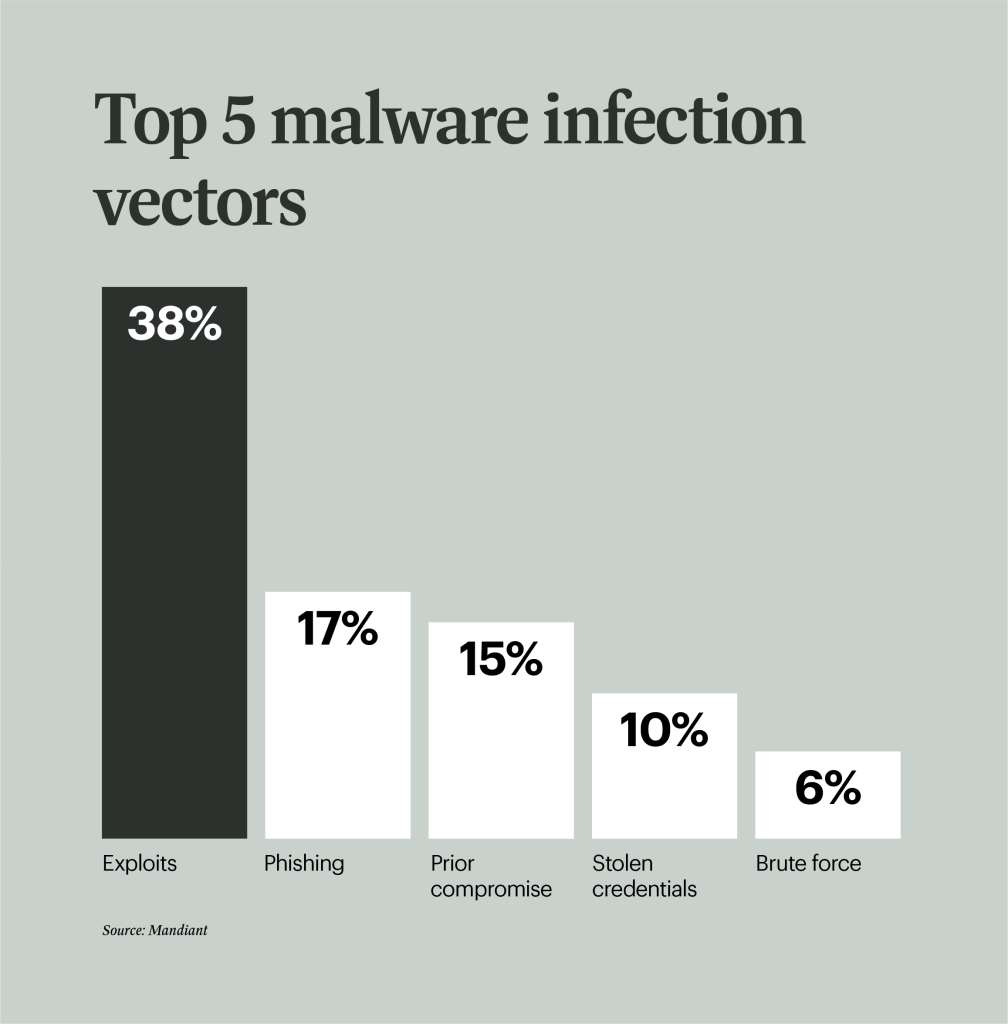
According to Mandiant’s M-Trends report for 2024, exploits were the top initial infection vector in 2023, used in 38% of attacks, followed by phishing (17%), prior compromise (15%), stolen credentials (10%), and brute force (6%) to round out the top 5.
Foundry
How malware spreads
You’ve probably heard the words virus, trojan, and worm used interchangeably. In fact, the terms describe three different kinds of malware, which are distinguished from each other by the process by which they reproduce and spread.
- A worm is a standalone piece of malicious software that reproduces itself and spreads from computer to computer. Worms’ creators build in knowledge of operating system vulnerabilities, and a worm program seeks these out on computers that it can reach from wherever it’s running and makes copies of itself on those insecure machines. Some of the very first worms were designed to copy themselves to floppy disks and other removable media, then copy themselves again when that disk was inserted into a new computer, but today most worms scan for vulnerable computers connected to their host via a corporate network or the internet.
- A virus is a piece of computer code that inserts itself within the code of another standalone program, then forces that program to take malicious action and spread itself. The infected program propagates itself in some of the same ways that a worm does, by searching for vulnerabilities on other computers it can reach via the internet or a local network. But the virus code is lurking inside programs that look legitimate, so there are other vectors by which it could it spread: if a hacker can infect an application at the source, an application that includes virus code could be available for download from open source repositories, app stores, or even the software maker’s own servers.
- A trojan is a program that cannot activate itself but masquerades as something the user wants and tricks them into opening it via social engineering techniques. Often trojans arrive as email attachments with names like “salary.xls” or “resume.doc”, with the malicious code lurking as a Microsoft Office macro. Once it’s running, one of its first jobs is to propagate itself, so it might hijack your email client and send out more copies of itself to potential victims.
Malware can also be installed on a computer “manually” by the attackers themselves, either by gaining physical access to the computer or using privilege escalation to gain remote administrator access.
How attackers hide malware
Why do cybercriminals use malware?
While some attackers might create malware as an intellectual exercise or for the thrill of destruction, most are motivated by financial gain. They could be looking for banking passwords or access to secrets they can sell or exploit, or they also could be looking to gain control of your computer and use it as a launching pad for a DDoS attack.
Once malware is executing on your computer, it can do a number of things, ranging from simply making it unusable to taking control out of your hands and putting your remote attacker in charge. Malware can also send back information about sensitive data to its creators.
Malware can also be part of a politically motivated attack. Hactivists might use malware in their campaigns against companies or governments, and state-sponsored hackers create malware as well. In fact, two high-profile malware waves were almost certainly started by national intelligence services: Stuxnet was created by the U.S. and Israel to sabotage Iran’s nuclear program, while NotPetya may have begun as a Russian cyberattack on Ukrainian computers that quickly spread beyond its intended targets (including back into Russia).
What are the types of malware?
There are a number of different ways of categorizing malware; the first is by how the malicious software spreads. We covered this in the section above on how malware infections happen.
Another way to categorize malware is by what it does once it has successfully infected its victim’s computers. There are a wide range of potential attack techniques used by malware:
- Spyware, as the name implies, is software that spieson your behavior as you use your computer, and on the data you send and receive, usually with the purpose of sending that information to a third party. A keylogger is a specific kind of spyware that records all the keystrokes a user makes—great for stealing passwords.
- A rootkit is malware that targets the underlying operating system to give the attacker ultimate control. It gets its name because it’s a kit of tools that (generally illicitly) gain root access (administrator-level control, in Unix terms) over the target system, and use that power to hide their presence.
- Adware is malware that forces your browser to redirect to web advertisements, which often themselves seek to download further, even more malicious software. As The New York Times notes, adware often piggybacks onto tempting “free” programs like games or browser extensions.
- Ransomware is a flavor of malware that encrypts your hard drive’s files and demands a payment, usually in Bitcoin, in exchange for the decryption key. Several high-profile malware outbreaks of the last few years, such as Petya, are ransomware. Without the decryption key, it’s mathematically impossible for victims to regain access to their files. So-called scareware is a sort of shadow version of ransomware; it claims to have taken control of your computer and demands a ransom, but actually is just using tricks like browser redirect loops to make it seem as if it’s done more damage than it really has, and unlike ransomware can be relatively easily disabled.
- Cryptojacking is another way attackers can force you to supply them with Bitcoin—only it works without you necessarily knowing. The crypto mining malware infects your computer and uses your CPU cycles to mine Bitcoin for your attacker’s profit. The mining software may run in the background on your operating system or even as JavaScript in a browser window.
- Malvertising is the use of legitimate ads or ad networks to covertly deliver malware to unsuspecting users’ computers. For example, a cybercriminal might pay to place an ad on a legitimate website. When a user clicks on the ad, code in the ad either redirects them to a malicious website or installs malware on their computer. In some cases, the malware embedded in an ad might execute automatically without any action from the user, a technique referred to as a “drive-by download.”
- A remote access trojan (RAT) is malware that gives an attacker control of a victim’s computer, similar to how legitimate remote access software allows helpdesk employees to take over users’ desktops to fix issues, essentially, rootkits that propagate like Trojans.
- A downloader is a type of Trojan that, as the name suggests, downloads other pieces of malware (sometimes in multiples).
- Polymorphic malware, also known as mutating malware, changes to avoid detection by antivirus and intrusion detection software. The Storm Worm is one such example.
Any specific piece of malware has both a means of infection and a behavioral category. So, for instance, WannaCry is a ransomware worm. And a particular piece of malware might have different forms with different attack vectors: for instance, the Emotet banking malware has been spotted in the wild as both a trojan and a worm.
A look at the Center for Internet Security’s top 10 malware offenders for Q4 of 2023 gives you a good sense of the types of malware in use today. NanoCore and Gh0st, are RATs, CoinMiner is cryptocurrency malware, and SocGholish and RogueRaticate are downloaders.
Does malware affect mobile devices?
In a word, yes, malware affects mobile devices and, according to Kaspersky, the threat is growing. In 2023, attacks on mobile devices increased 52% over the prior year, with adware accounting for 40.8% of all threats detected.
Pegasus, mobile spyware that targets both iOS and Android, is on CIS’s top malware offenders list. Some other common types of mobile malware are banking malware, mobile ransomware, and mobile adware.
52%
From 2022 to 2023, attacks on mobile devices increased 52%, making up 40.8% of all threats detected, according to antivirus vendor Kaspersky.
Mobile malware in the news:
- Over 60,000 Android apps infected with adware-pushing malware
- Guerrilla malware is preinfected on 8.9 million Android devices, Trend Micro says
- Espionage campaign loads VPN spyware on Android devices via social media
- Android-based banking Trojan Nexus now available as malware-as-a-service
- Russia points finger at US for iPhone exploit campaign that also hit Kaspersky Lab
- Apple patches exploits used in spy campaign ‘Operation Triangulation’
Identifying signs of malware
It’s fully possible—and perhaps even likely—that your system will be infected by malware at some point despite your best efforts. How can you tell for sure? Security expert Roger Grimes has a great guide on telltale signs you’ve been hacked, which can range from a sudden decline in your computer’s performance to unexpected movements of your mouse pointer. He’s also written a deep dive into how to diagnose your how to detect malware on Windows PCs that you might find helpful.
When you get to the level of corporate IT, there are also more advanced visibility tools you can use to see what’s going on in your networks and detect malware infections. Most forms of malware use the network to either spread or send information back to their controllers, so network traffic contains signals of malware infection that you might otherwise miss; there are a wide range of network monitoring tools out there, with prices ranging from a few dollars to a few thousand. There are also SIEM tools, which evolved from log management programs; these tools analyze logs from various computers and appliances across your infrastructure looking for signs of problems, including malware infection. SIEM vendors range from industry stalwarts like IBM and HP Enterprise to smaller specialists like Splunk and Alien Vault.
How to prevent malware
Much of malware prevention comes down to good cyber hygiene. At minimum, you should be taking these 7 steps:
- Provide regular security awareness training for users
- Have a solid patch management program
- Keep your software updated
- Keep your asset inventory up-to-date
- Perform regular vulnerability assessments
- Monitoring network traffic
- Keep good backups
With spam and phishing email consistently one of the primary vectors by which malware infects computers, one of the best ways to prevent malware is make sure your email systems are locked down tight—and your users know how to spot danger. We recommend a combination of carefully checking attached documents and restricting potentially dangerous user behavior—as well as just familiarizing your users with common phishing scams so that their common sense can kick in.
When it comes to more technical preventative measures, there are a number of steps you can take, including keeping all your systems patched and updated, keeping an inventory of hardware so you know what you need to protect, and performing continuous vulnerability assessments on your infrastructure. For ransomware attacks in particular, one way to be prepared is to always make backups of your files, ensuring that you’ll never need to pay a ransom to get them back if your hard drive is encrypted.
Malware protection
Antivirus software is the most widely known product in the category of malware protection products; despite “virus” being in the name, most offerings take on all forms of malware. While high-end security pros dismiss it as obsolete, it’s still the backbone of basic anti-malware defense. Today’s best antivirus software is from vendors Kaspersky Lab, Symantec and Trend Micro, according to recent tests by AV-TEST.
When it comes to more advanced corporate networks, endpoint security offerings provide defense in depth against malware. They provide not only the signature-based malware detection that you expect from antivirus, but anti-spyware, personal firewall, application control and other styles of host intrusion prevention. Gartner offers a list of its top picks in this space, which include products from Cylance, CrowdStrike, and Carbon Black.
How to detect malware
It’s fully possible—and perhaps even likely—that your system will be infected by malware at some point despite your best efforts. How can you tell for sure? Security expert Roger Grimes has a great guide on telltale signs you’ve been hacked, which can range from a sudden decline in your computer’s performance to unexpected movements of your mouse pointer. He’s also written a deep dive into how to diagnose your PC for potential malware that you might find helpful.
When you get to the level of corporate IT, there are also more advanced visibility tools you can use to see what’s going on in your networks and detect malware infections. Most forms of malware use the network to either spread or send information back to their controllers, so network traffic contains signals of malware infection that you might otherwise miss; there are a wide range of network monitoring tools out there, with prices ranging from a few dollars to a few thousand. There are also SIEM tools, which evolved from log management programs; these tools analyze logs from various computers and appliances across your infrastructure looking for signs of problems, including malware infection. SIEM vendors range from industry stalwarts like IBM and HP Enterprise to smaller specialists like Splunk and Alien Vault.
Malware protection
Antivirus software is the most widely known product in the category of malware protection products; despite “virus” being in the name, most offerings take on all forms of malware. While high-end security pros dismiss it as obsolete, it’s still the backbone of basic anti-malware defense.
When it comes to more advanced corporate networks, endpoint security offerings provide defense in depth against malware. They provide not only the signature-based malware detection that you expect from antivirus, but anti-spyware, personal firewall, application control and other styles of host intrusion prevention. CSO offers advice on how to choose an endpoint security offering, and gives an outline of the top vendors, which include BitFinder, Malwarebytes, and Sophos.
Malware removal
How to remove malware once you’re infected is in fact the million dollar question. Malware removal is a tricky business, and the method can vary depending on the type you’re dealing with. CSO has information on how to remove or otherwise recover from rootkits, ransomware, and cryptojacking. We also have a guide to auditing your Windows registry to figure out how to move forward.
If you’re looking for tools for cleansing your system, Tech Radar has a good roundup of free offerings, which contains some familiar names from the antivirus world along with newcomers like Malwarebytes.
Malware trends
You can count on cyber criminals to follow the money. They will target victims depending on likelihood of delivering their malware successfully and size of potential payout. If you look at malware trends over the past few years, you will see some fluctuation in terms of the popularity of certain types of malware and who the most common victims are—all driven by what the criminals believe will have the biggest ROI.
The June, 2024 edition of BlackBerry’s Global Threat Intelligence Report found that new malware increased 40% in the first quarter of 2024 over the previous quarter and despite high-profile takedowns ransomware remains a significant threat, with LockBit, Hunters International, and 8Base being the most active groups globally.
Recent research from cybersecurity firm Mandiant, based on investigations of targeted attack activity the company conducted in 2023, indicate some interesting shifts in malware tactics and targets. These include:
- Attackers are very focused on avoiding detection with the goal of remaining on networks as long as possible. Despite this, average dwell time dropped from 16 days in 2022 to 10 days in 2023. This can be attributed to an increase in ransomware attacks, which typically have a lower dwell time than other types of malware.
- Ransomware comprised 23% of Mandiant investigations in 2023, up from 18% in 2022
- Attackers engaging in espionage and financially-motivated attacks continue to leverage zero-day vulnerabilities. Vulnerabilities in MOVEit file transfer, Oracle E-Business Suite, and Barracuda Email Security Gateways were the most leveraged by attackers.
- More than one-third of attacks (36%) were financially motivated.
- Financial services firms were the most highly targeted by attackers, comprising 17.3% of Mandiant’s investigations, followed by business and professional services (13.3), high tech (12.4%), retail and hospitality (8.6%), and healthcare (8.1%).
This article, originally written in 2019, has been updated to reflect current trends.
More on malware
- 9 types of malware and how to recognize them
- CISA opens its malware analysis and threat hunting tool for public use
- Surge in “hunter-killer” malware poses significant challenge to security teams
- Malware variability explained: Changing behavior for stealth and persistence
- DNS data shows one in 10 organizations have malware traffic on their networks










